The reason I'm writing this is because Totemo makes ZERO resources available to the public on how to manage this terrible product and they force you to open a ticket for everything...job security I guess.
Unlike most other appliances, web servers, etc. the cert request process on the Totemo Gateway doesn't include the private key, which is needed later for the new cert import. You'd think if it were required for the import, it would be included in the request, but as I said above, the product is garbage.
So you need to export the private key manually and then jump through some hoops to merge it with your new cert from your CA; that requires some OpenSSL work, which is a bit of a pain.
First, start your cert request.
Expand Certificates > Own Server Certificates > hit the "New HTTPS cert" button.
Fill out your org info and download/save the req on your local machine.
Send the req to your public CA and you should get a cert.cer and intermediate.pem back.
Next, export the private key
**Note** The private key is stored in the Totemo database (either locally or in a standalone DB, depending on how you have it set up)
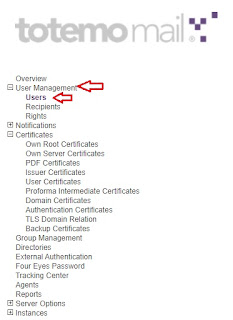
You can export the private key from your current HTTPS cert or from a current user.
To export the private key from the current HTTPS cert, Expand Certificates > Own Server Certificates
Click the cert icon > go to the Details tab > hit the "export with pr. key" button
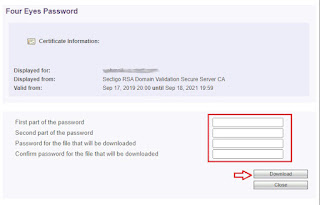
Enter your first and second "four eyes password"
Enter your password that will be set on the private key file, twice
Hit "Download"
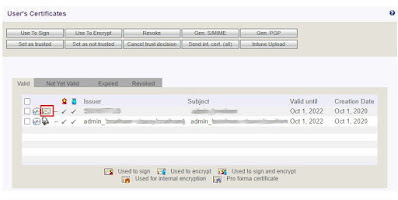
Click the certificate management (keys icon) for an active user > click the cert icon > Details tab > "export with pr. key" button
Enter your first and second "four eyes password"
Enter your password that will be set on the private key file, twice
Hit "Download"
A gotcha here: make sure you use a strong password on the export (capital, lowercase, number and special character, and at least 8 characters long). There is no "help" prompt on the Totemo for this, it just throws a stupid error that says "error connecting to database" which doesn't mean anything at all.
***Note*** In order for the "export with pr. key" button to be visible in the above steps, you first need to set your "Four Eyes Password" under the Four Eyes Password section...set both passwords; they can be anything, but make them strong. If they haven't been set yet, leave the box empty and hit the "Continue" button to set them.
Once you have your private key exported, fire up OpenSSL, which should be located in C:\Program Files\OpenSSL-Win64
If you don't have it installed you can grab it from here
First we need to extract the key file. Copy your privatekey.p12 file to the C:\Program Files\OpenSSL-Win64\bin directory then run the following command:
openssl pkcs12 -in privatekey.p12 -out totemokey.key -nodes -nocerts
***Note*** Change privatekey.p12 to the filename of your p12
Next, copy your totemokey.key, cert.crt and intermediate.pem files to the C:\Program Files\OpenSSL-Win64\bin directory
Now we'll merge the files by running the following command:
openssl pkcs12 -export -out totemo.pfx -inkey totemokey.key -in cert.crt -certfile ntermediate.pem
***Note*** Change to totemo.pfx, totemokey.key, cert.crt, ntermediate.pem to the filenames of your certs
You will be prompted to create a password; this can be anything, but I suggest make it strong.
Once it completes, you will have a brand new pfx file, which you will import into the Totemo
Expand Certificates > Own Server Certificates
In the dropdown, select "Import certificate for HTTPS"
Hit the "choose file" button and select your new .pfx
Enter your password you set on the pfx in OpenSSL
Hit OK
If it goes correctly, it will list your new cert.









No comments:
Post a Comment